As a technical founder, you need controls that work reliably without the complexity of enterprise stacks. This playbook is a compact, battle-tested checklist to stop brute-force and credential stuffing attacks on WordPress. It focuses on pragmatic, low-overhead measures you can implement today, with guided choices for plugins, server tweaks, monitoring, and an incident response plan you can follow when an attack hits.
Why attackers focus on WordPress logins
WordPress powers a large portion of the web, and logins are a low-friction attack surface: many sites use weak passwords, reused credentials, or lack multifactor protection. Attackers run distributed credential stuffing campaigns and automated brute-force bots because even a small success rate yields access. Your goal is to make authenticated compromise expensive and noisy, so automated attacks fail and human intervention is needed — which you detect and respond to. Focused brute-force protection increases the cost-per-attack and reduces successful compromises to near-zero for well-hardened sites.
Quick baseline: essential defenses and how they compare
Before we dive into configuration, here’s a compact comparison to help you choose which controls to prioritize based on impact and maintenance cost.
| Control | Primary benefit | Operational cost | When to pick |
|---|---|---|---|
| Rate-limiting / Login throttling | Stops automated rapid attempts | Low — single plugin or server rule | Always; first line of defense |
| Two-factor authentication (MFA) | Blocks credential reuse | Low-medium — user training required | High-value sites and admin accounts |
| IP blacklists & WAF | Blocks known malicious sources | Medium — tuning to avoid false positives | When attacks originate from repeat offenders |
| CAPTCHA | Deters simple bots | Low — can impact UX | Use for high-volume public login forms |
| Password policy & leak detection | Reduces success of credential stuffing | Low — integration with common plugins | Always; especially when users self-register |
Implementing defenses — practical checklist
Below is a checklist you can work through in a single maintenance window. Each item has an actionable example so you can apply it without extra research. The checklist is ordered by impact and ease of implementation for rapid brute-force protection gains.
- Enable rate-limiting on logins (plugin or server).
Example: configure a plugin to allow 5 failed attempts per 10 minutes, then lock for 30 minutes. If using Nginx, add a limit_req rule at the server block (example below). - Enforce MFA for admin/editor accounts.
Use TOTP tokens (Authy/Google Authenticator) rather than SMS; require MFA for users with edit/publish privileges first. - Deploy a WAF or host-level firewall.
Add rules to block known bot patterns and the /xmlrpc.php abuse vectors. Whitelist management IPs if you have static addresses. - Install a password policy plugin and leak checks.
Minimum length 12, require mixed-case and a symbol, block commonly leaked passwords. For users failing checks, force MFA and schedule a password reset. - Hide or rename default /wp-login.php.
Note: renaming is security-through-obscurity—use it with rate-limits and MFA, not alone. - Log failed logins centrally.
Forward webserver and plugin logs to your monitoring stack and set alerts on spikes. - Audit users weekly.
Remove stale admin/editor accounts, and rotate credentials for high-privilege users.
Choosing plugins — quick rules
Pick plugins with active maintenance, clear changelogs, and limited permissions. Test any login-protection plugin in staging to prevent accidental lockouts. Recommended configuration checklist:
- Limit-to-5-fails / 10-minutes → lock 30 minutes.
- MFA enforced for roles: administrator, editor, and any custom high-privilege roles.
- Password policy: min 12 chars, block top 10,000 leaked passwords list.
- Session management plugin or use core key rotations to invalidate sessions after compromise.
Use your Documentation and plugin change logs to validate behavior before enabling site-wide.
Server-level protections — examples
Prefer server-level rate-limiting where possible: Nginx’s limit_req stops bad traffic before PHP runs. Add fail2ban rules to ban IPs that trigger repeated failures. These controls are effective and have a low performance cost compared to application-only solutions.
Example Nginx snippet (put in http or server block):
# limit to ~6 requests/minute for login path
limit_req_zone $binary_remote_addr zone=login:10m rate=6r/m;
location = /wp-login.php {
limit_req zone=login burst=2 nodelay;
proxy_pass ...;
}
Simple fail2ban idea: create a filter matching repeated POSTs to /wp-login.php and add a jail to ban for 1 hour after 5 failures. Tweak thresholds to balance false positives.
Password policy and leak detection
Enforce strong passwords and integrate a breached-password check on registration and password change flows. If you must support legacy users, require MFA and schedule a forced password reset for accounts that fail leak checks. Example settings:
- Minimum password length: 12
- Disallow passwords found in breach lists
- Force password rotation for accounts dormant > 9 months
Myth vs. Reality
Attack mitigation is full of assumptions. Here’s a short myth-vs-reality breakdown to recalibrate decisions.
Myth vs Reality
- Myth: “CAPTCHA alone stops credential stuffing.” Reality: CAPTCHAs deter simple bots but not sophisticated farms; combine with rate-limiting and MFA.
- Myth: “Strong passwords are enough.” Reality: Password reuse and leaked credentials make MFA essential for admin roles.
- Myth: “Locking accounts after a few failures won’t break UX.” Reality: Lockouts must be balanced—use gradual throttling and clear unlock paths to avoid blocking legitimate users.
Incident response playbook for authentication attacks
When an attack happens, speed and discipline matter. This subsection gives a short incident playbook you can follow immediately after detection.
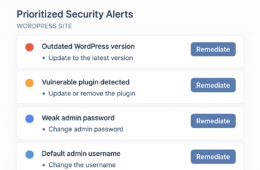
Immediate containment
- Temporarily increase lockout sensitivity and enable site-wide maintenance mode if admin access is threatened.
- Block offending IPs at the network edge and enable emergency WAF rules to drop abusive traffic (temporary allowlists for staff only).
- Force password resets and require MFA re-enrollment for all admin/editor accounts.
- Rotate WordPress authentication keys/salts in wp-config.php to invalidate existing sessions if you suspect account theft.
Forensics and recovery
Capture logs (access, PHP, and plugin logs) for the attack window and preserve a timestamped snapshot. Check for successful logins, changes to admin users, new plugins/themes, and unexpected file modifications. If you detect a compromised account, revoke sessions, rotate keys, and restore site files from a known-clean backup.
Sample WP-CLI steps to audit and recover:
# list users to audit wp user list --role=administrator # force set a temporary password for user ID 2 (replace with real ID) wp user update 2 --user_pass='Temp$tr0ngP@ss123' # rotate salts: edit wp-config.php with new generated keys
After rotation, instruct users to re-enroll MFA and update passwords using the policy you set.
Post-incident follow-up
Document indicators of compromise, update detection rules to surface similar attacks earlier, and schedule a post-mortem to tighten policies. Feed findings into your monitoring so the next event is detected faster. Update your runbooks and the Battle-Tested WordPress Security Checklist to capture lessons learned.
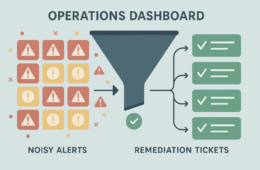
Monitoring, alerts, and recovery
Monitoring turns hardening into a living system. Log failed logins, track lockouts, and set alerts for abnormal spikes. Example alert thresholds to start with:
- Failed login attempts > 50 in 5 minutes — alert ops team.
- More than 10 unique IPs attempting logins to a single account in 10 minutes — investigate for credential stuffing.
- Lockouts > 20 in 15 minutes — possible botnet targeting; escalate to block lists.
Pair automated alerts with a simple runbook that tells on-call staff which steps to take. Keep the runbook short and action-oriented: block IP ranges, enable stricter throttling, rotate salts, and start an incident ticket. For broader recovery and monitoring guidance, use the Battle-Tested WordPress Security Checklist.
Quick comparison: low-effort combos that work
Combine low-friction measures to get high protection with minimal overhead:
- Rate-limiting + MFA = excellent protection for admin accounts.
- WAF + breach-password checks = good protection for public user logins.
- Server-level throttling + plugin lockout = effective against distributed bots.
Practical tasks you can complete in two hours
- Install and configure a rate-limiting or lockout plugin; test with a staging account. Set to 5 fails / 10 minutes, 30-minute lockout.
- Enable TOTP-based MFA for all admin/editor accounts and verify recovery codes are stored securely.
- Add server-level fail2ban or Nginx rate-limiting rules and restart services during a maintenance window.
- Audit admin users and remove stale or unused accounts; rotate high-privilege credentials and salts.
Where to go next
Make these configurations routine: include them in deploy checklists and onboarding docs. If you want step-by-step assistance or evaluated configurations tailored to your stack, consider professional help from Hack Halt Inc. — they focus on practical, founder-friendly security without enterprise bloat. Explore the Security Hub for tools, read the Blog for ongoing hardening guidance, or view other resources like Business Cyber Defense 2025 and Latest Zero-Day Vulnerabilities Every Business Should Know.
FAQ
- Q: Will enabling MFA break my users’ login flow?
- A: MFA adds a step, but TOTP apps are widely supported and easy to adopt. Roll it out in phases: require MFA for admins first, then for higher-risk user groups, and provide recovery options for non-technical users. Document the workflow in your onboarding materials and link to Register or support pages as needed.
- Q: Should I rely on CAPTCHA as my main defense?
- A: No. CAPTCHA helps against simple bots but does not stop credential stuffing using human-solved farms or sophisticated automation. Use CAPTCHA as a layer with rate-limiting and MFA.
- Q: How can I avoid locking out legitimate admins when increasing sensitivity?
- A: Use staged throttling (gradual slowdowns before full lockout), whitelist management IPs when possible, and provide clear unlock/rescue flows (secondary email or admin contact). Test changes in staging first and document rollback steps like temporarily disabling the plugin or restoring wp-config.php.
- Q: What logs should I capture during an attack?
- A: Capture web server access logs, PHP error logs, plugin authentication logs, and any WAF logs. Preserve timestamps and IPs, and snapshot the site or database if you suspect modification. Forward critical logs to your centralized log store so they survive server rebuilds.
For help integrating brute-force protection into your broader security program or to book a reviewed hardening session, visit Contact, check Terms & Conditions, or review pricing on the Pricing page. If you’d like to stop here and subscribe to updates, see Welcome!, or explore product Docs on Documentation. Good brute-force protection is achievable with predictable, repeatable steps — make it part of your routine maintenance and incident plans.