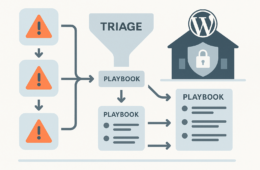
For IT generalists responsible for uptime, patching, and incident response on WordPress sites, security isn’t just a checkbox—it’s a mission-critical operation. This battle-tested checklist playbook guides you through concrete, tactical steps to reduce the blast radius of incidents by combining robust monitoring with swift recovery playbooks. By applying these hardened practices, you can keep your WordPress sites resilient and responsive to real-world threats.
1. Understand Your WordPress Security Posture
Start by assessing your current environment. Know which plugins, themes, and WordPress versions you’re running and their update status. A clear understanding of your environment sets the foundation for effective security measures.
1.1 Inventory and Version Control
Identify all active plugins and themes and ensure they are updated to the latest secure versions. Use automated tools where possible to reduce human error. Here’s a practical approach:
- Export a list of all installed plugins and themes along with their versions.
- Check compatibility notes and security advisories before updating.
- Schedule weekly automated update checks and generate reports for manual review.
This ongoing inventory helps you detect outdated or abandoned plugins that pose risks.
1.2 User Roles and Permissions Audit
Review user roles carefully. Remove inactive users and apply the principle of least privilege to limit admin access. Limit blast radius if an account is compromised by:
- Regularly exporting user role reports, focusing on Administrator, Editor, and Author roles.
- Enabling multi-factor authentication (2FA) particularly for all users with elevated privileges.
- Implementing strict password policies and forcing periodic password resets.
- Auditing login history to identify uncommon access patterns.
1.3 Baseline Monitoring Capabilities
Enable and verify monitoring for typical security events—login attempts, file changes, plugin updates. Link this strategically with your existing IT monitoring dashboards by following these steps:
- Deploy plugins or external agents that capture detailed logs of all administrative events.
- Integrate WordPress logs into centralized log management systems like SIEMs if available.
- Define thresholds for anomalous activities such as sudden spikes in login failures.
- Periodically review alerts and tune detection rules to minimize false positives.
2. Hardening WordPress: Tactical Checklist
Implement these key hardening steps to decrease attack surface and improve resilience:
- Disable file editing from the WordPress dashboard by setting
define('DISALLOW_FILE_EDIT', true);inwp-config.php. This prevents attackers from injecting malicious code through the UI. - Enforce strong password policies by using plugins that require complex password criteria and expiration periods.
- Enable two-factor authentication (2FA) for all users, especially administrators and editors, to add an additional verification layer during login.
- Limit login attempts with threshold-based blocking to mitigate brute force attacks. For example, block an IP after 5 failed attempts within 10 minutes.
- Employ HTTPS everywhere with valid SSL/TLS certificates to encrypt data in transit and prevent session hijacking.
- Regularly back up files and databases to secure, isolated locations — store offsite or in cloud storage with versioning enabled.
- Disable directory browsing via
.htaccessor server configuration to prevent information disclosure. - Remove or disable unused themes and plugins to reduce exposure.
- Use security-focused plugins that provide firewall, malware scanning, and login monitoring capabilities.
Refer to our Security Hub for detailed guides on each of these hardening tactics, including configuration examples and recommended plugin lists.
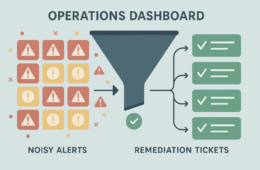
3. Real-Time Monitoring Strategies
Effective monitoring is the heart of blast radius reduction. Consider these comprehensive strategies:
3.1 Utilize Logs and Alerts
Monitor web server access, WordPress logs, and plugin-specific logs for anomaly detection. Implement the following:
- Log all login attempts, password reset requests, and admin-area access.
- Track file changes in critical directories such as
/wp-content/plugins/and/wp-content/themes/. - Configure alerts to notify administrators immediately of suspicious behaviors such as multi-location logins or rapid file changes.
- Employ log correlation tools to detect patterns that indicate reconnaissance or ongoing attacks.
3.2 Integrate Threat Intelligence
Plug into feeds such as the Global Threat Intelligence Network to stay informed about emerging vulnerabilities and attack vectors targeting WordPress. Implementation tips include:
- Subscribe to real-time threat updates focusing on WordPress CVEs and plugin vulnerabilities.
- Automate IP and domain blacklisting based on threat feed data.
- Conduct threat hunting exercises aligned with intelligence insights on your WordPress environment.
3.3 Regular Malware Scanning
Schedule scans with trusted tools to catch intrusive code early. Incorporate automated remediation where possible, following these best practices:
- Perform deep scans of all site files and database content.
- Enable scheduled scans at times when site traffic is low to minimize impact.
- Audit plugin and theme directories for suspicious or unknown files.
- Use quarantine features to isolate detected malware pending further analysis.
4. Recovery Playbooks to Minimize Damage
When breaches happen, how fast and structured your recovery is determines your incident blast radius. Follow this detailed playbook for an effective response:
| Phase | Key Actions | Tools/Resources |
|---|---|---|
| Identification |
|
WordPress logs, security plugins, IDS |
| Containment |
|
Login lockdown plugins, firewall rules |
| Eradication |
|
Antimalware tools, manual code review |
| Recovery |
|
Backup software, update management |
| Post-Incident Review |
|
Incident documentation templates, policy updates |
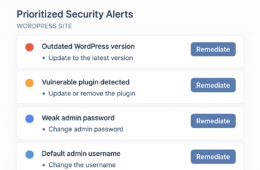
5. Myth vs. Reality: Common WordPress Security Misconceptions
Myth
“If I keep my plugins updated, my site is 100% secure.”
Reality
While updates are critical, they’re just one component. Attackers exploit overlooked vectors like default usernames, weak passwords, and missing monitoring. Protecting your site demands a comprehensive approach—including continuous monitoring, strict access controls, and well-rehearsed recovery playbooks—to truly reduce incident impact.
6. Incident Response: A Tactical Walkthrough
Imagine receiving alerts of a sudden spike in failed login attempts on your WordPress site. Follow this operational flow to minimize damage:
- Identification: Initiate incident identification by checking logs and plugins such as login audit tools to ascertain attack patterns and targeted accounts.
- Containment: Temporarily disable access for affected users, apply CAPTCHA challenges or IP blocks to mitigate ongoing attacks.
- Eradication: Scan for unauthorized backdoors, suspicious redirects, and injected code; remove or quarantine findings.
- Recovery: Restore the latest verified clean backup, update core and plugins, and enforce password resets for all users, especially administrators.
- Post-Incident Review: Conduct a thorough assessment, adjust monitoring and access controls, and update your recovery playbooks to incorporate lessons learned.
Our detailed documentation at Hack Halt Inc. provides operators with step-by-step templates and tools tailored specifically for WordPress incident response workflows.
Practical WordPress Security Hardening Checklist
- Update WordPress core, plugins, and themes on a weekly schedule or immediately after critical patches are released.
- Set up automated backups with verified restoration tests every month to ensure recoverability.
- Enforce strong passwords and enable two-factor authentication for all user accounts.
- Limit login attempts with IP throttling and enable automated blocking for repeated failures.
- Disable file editing in the WordPress admin dashboard to prevent code injection via the UI.
- Monitor logs daily and configure alerts for activities such as multiple failed logins, unexpected file changes, and plugin updates.
- Conduct quarterly incident response exercises simulating attacks to test and refine your recovery playbooks.
- Remove any unused themes or plugins immediately to minimize potential vulnerabilities.
- Review user access quarterly, especially administrators, and revoke or downgrade unused accounts.
FAQ
Q1: How often should I update my WordPress site?
Ideally, update weekly or immediately upon seeing critical security patches. Rapid updates close known vulnerabilities before attackers can exploit them. Automate update notifications to maintain consistent patching rhythms.
Q2: What types of monitoring should I deploy?
Use a combination of login monitoring, file integrity checks, malware scans, and threat intelligence integration for comprehensive coverage. This layered approach enhances detection and reduces false negatives. Consider setting up alerts for:
- Multiple failed login attempts from the same IP.
- Unauthorized file changes in plugin or theme directories.
- Sudden spikes in outbound traffic indicating possible command and control activity.
Q3: How can I reduce downtime during incident recovery?
Maintain recent clean backups and automate restoration processes to minimize manual intervention. Keep recovery playbooks updated and conduct regular drills with your team to ensure familiarity and speed during real incidents.
Q4: What internal resources can support WordPress incident response?
Platforms like the Security Hub offer comprehensive guides and tools. Coordinate with your organization’s cloud infrastructure and networking teams if your WordPress site forms part of a broader digital ecosystem. Clear communication channels and defined roles enhance response effectiveness.
At Hack Halt Inc., we emphasize the importance of turning security theory into operational mastery. Combining monitoring, hardening, and recovery reduces incident blast radius and fortifies uptime reliability for your WordPress environment. Begin your defensive journey with this checklist playbook and keep your site resilient well beyond 2026.
For a quick start, visit our Welcome! page and register at Register to access exclusive updates and tools. Should you need assistance or wish to upgrade your protection, contact us anytime via our Contact page.